Friend sent me a strange message she got with the following link:
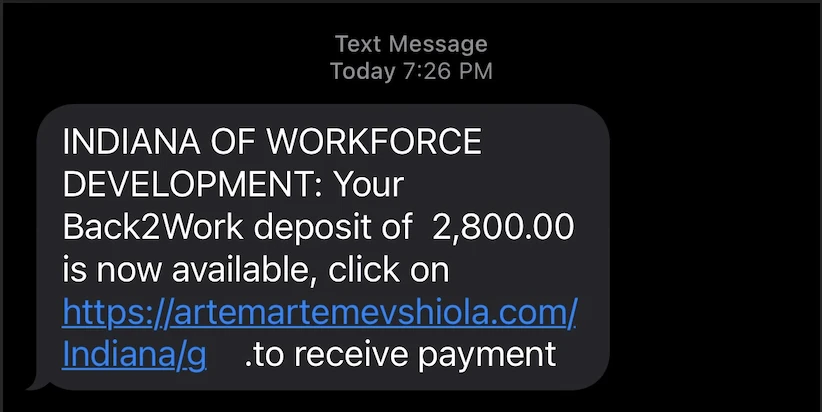
Thanks government, for giving me my money back on some strange link
Attempt 1: www
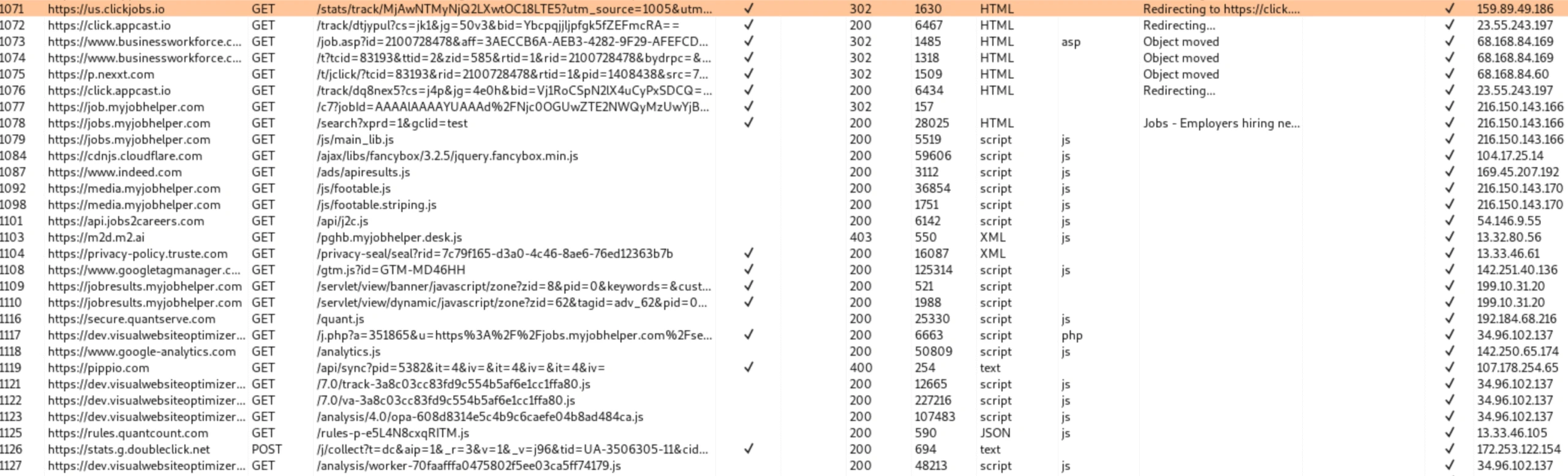
I booted into my REMnux VM and turned on Burp suite to intercept the traffic. If you leave off the trailing slash (like in the text above), it just redirects to /Indiana/g/ then proceeds as following:
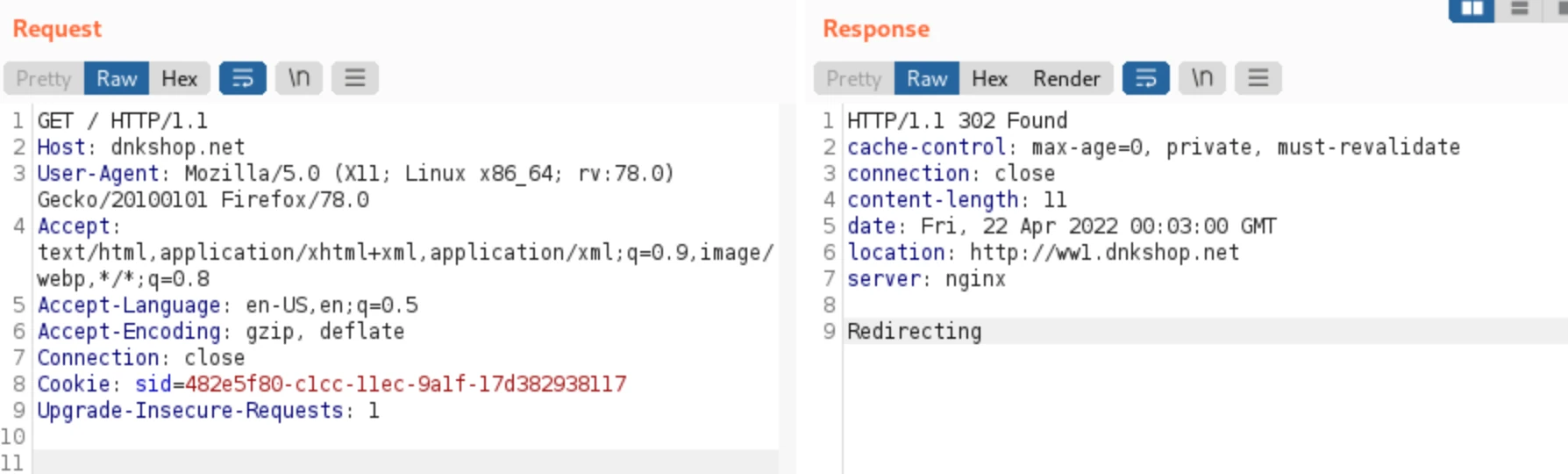
Step 1: Link redirects to dnkshop
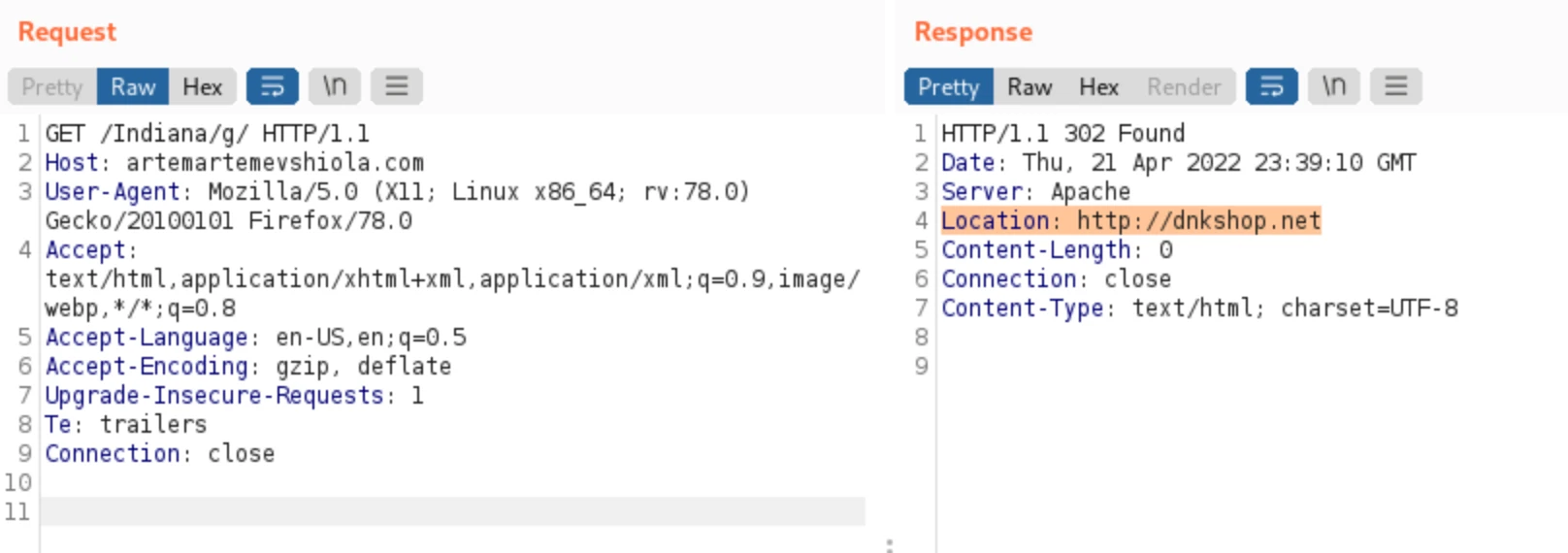
Step 2: dnk shop redirects to itself, but now with a sid cookie and a JWT token
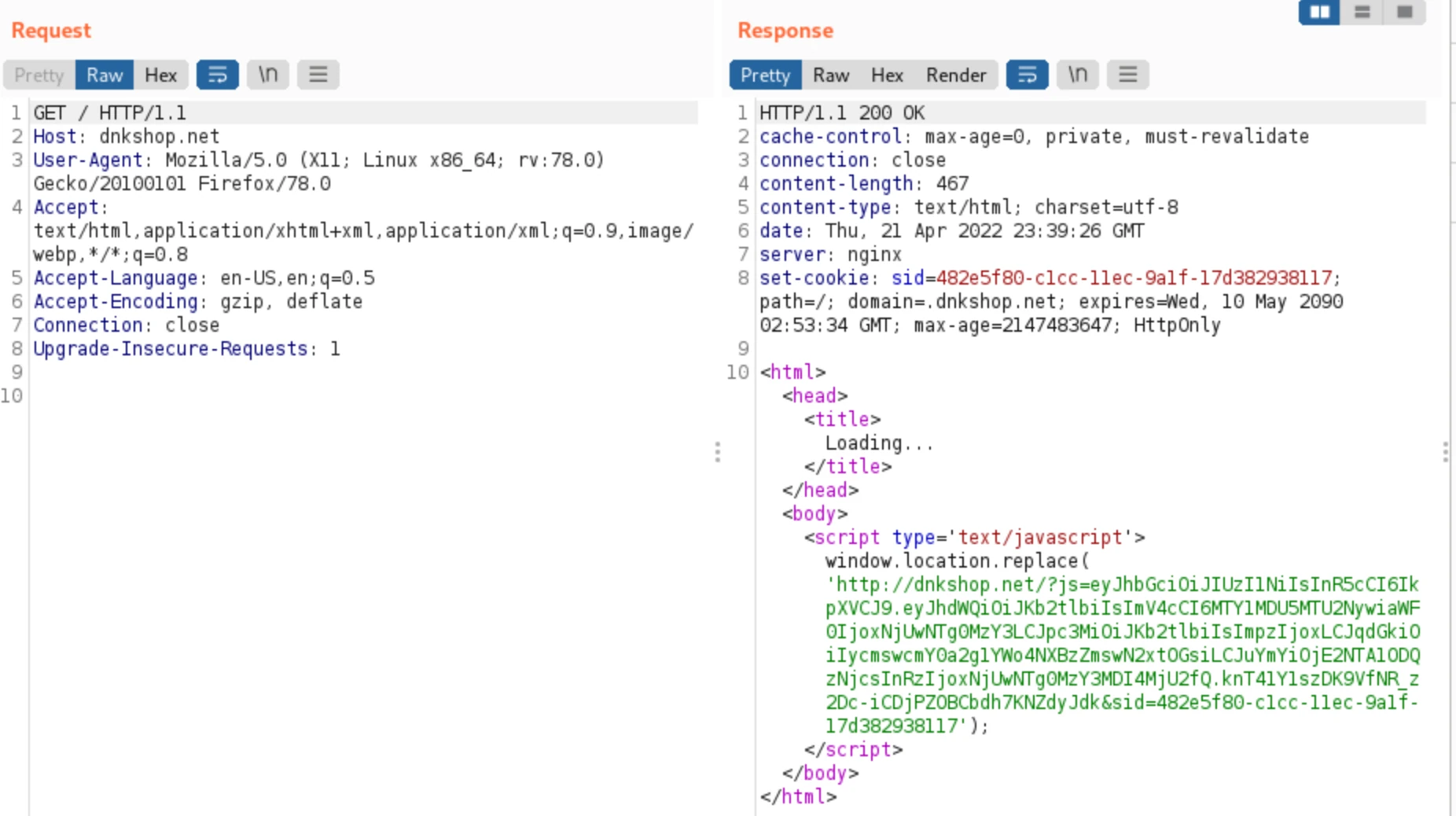
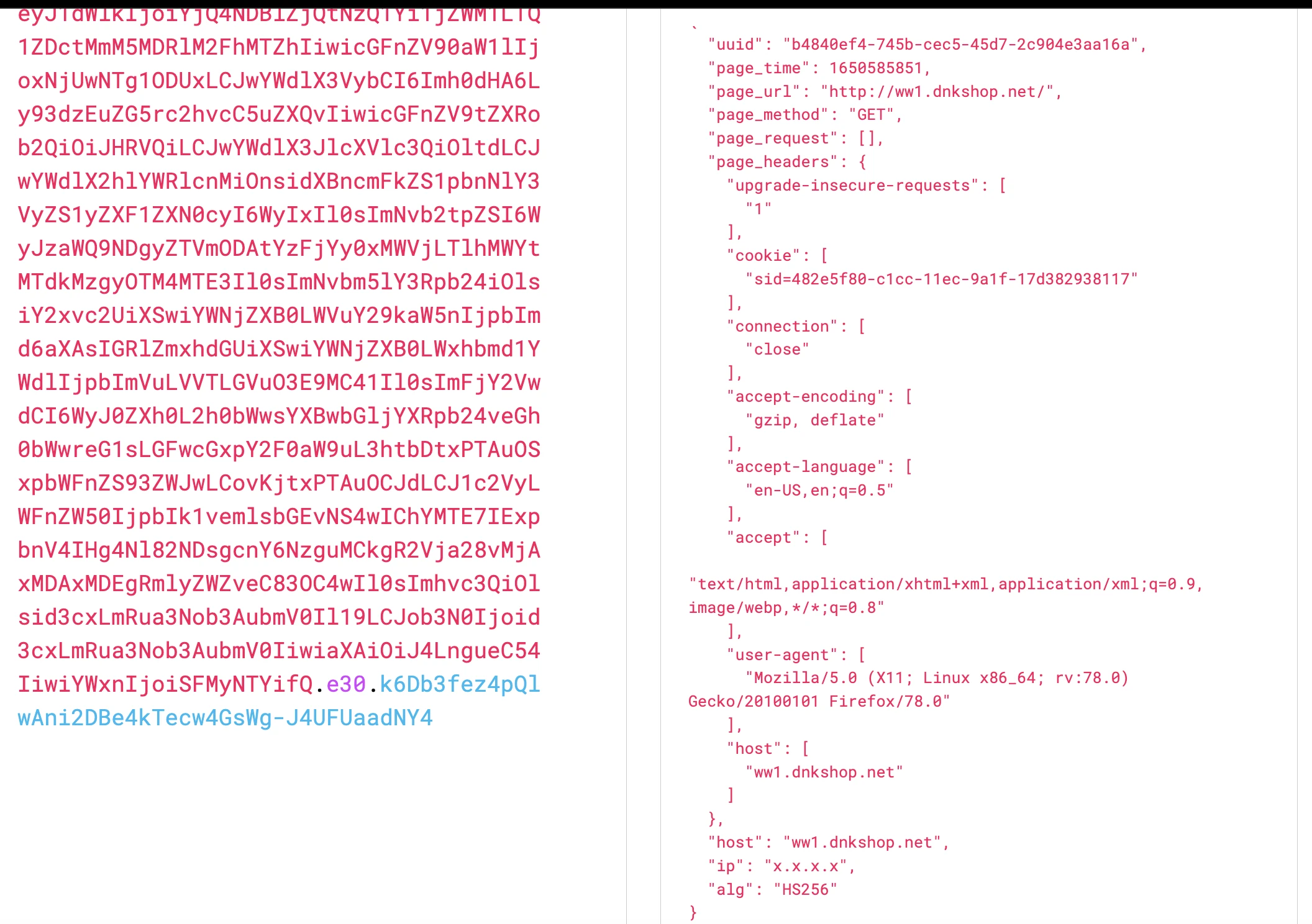
I decoded the JWT token, it was created, presumably, by the library Joken. This is a library for a programming language called Elixir.
JWT decoded
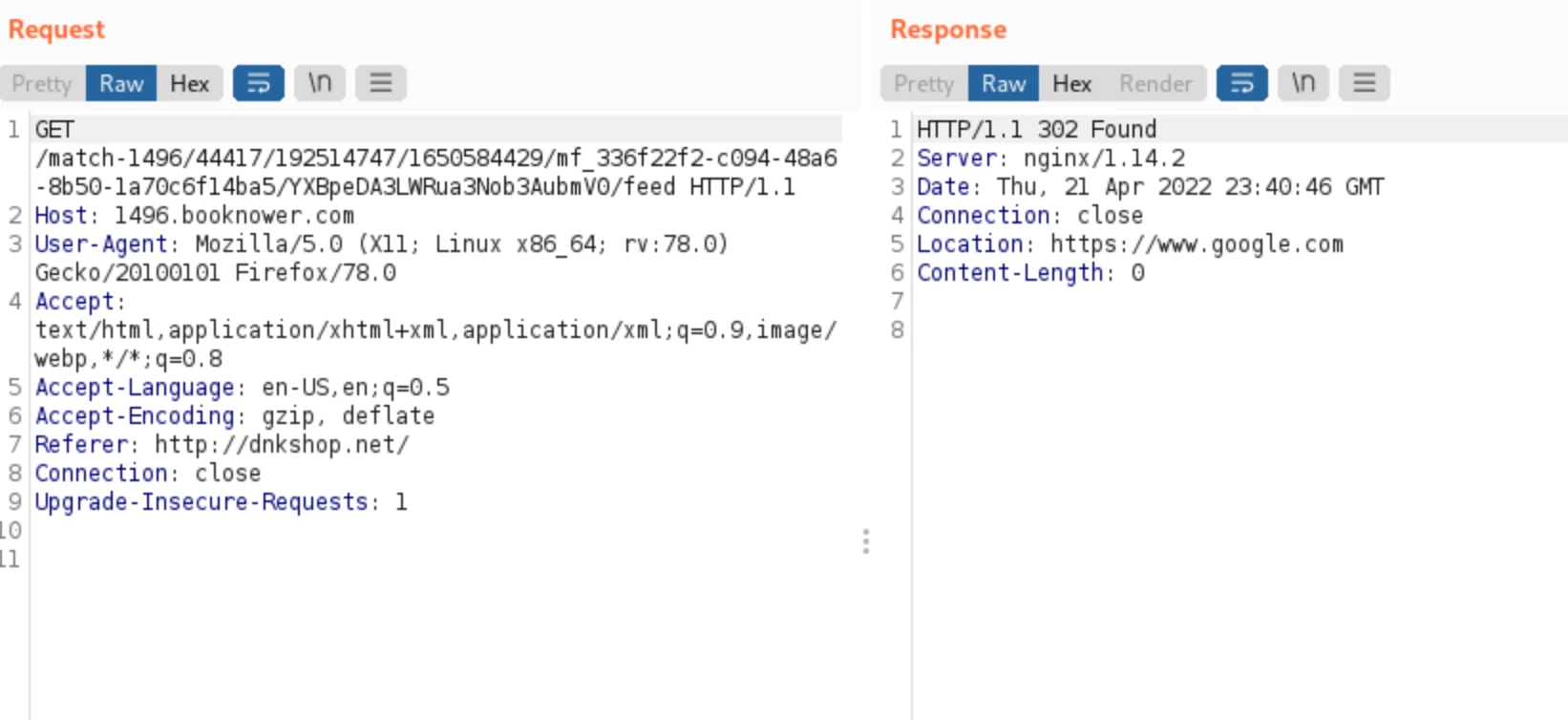
With the token and cookie set, it just immediately redirects you to a new booknower

Another redirect
Finally, this URL just redirects back to google.:
I tried to mess with the parameters of the booknower URL but I kept getting 503 errors like the server was down. I noticed if I retired the URL, the sequence was now different.
Attempt 2: ww1
In this attempt, it navigated me to ww1
This time the contents of the page were way different. It set an adblock cookie and loaded a parking.2.86.1.js file. It also contains another token/base64 string to a window.park
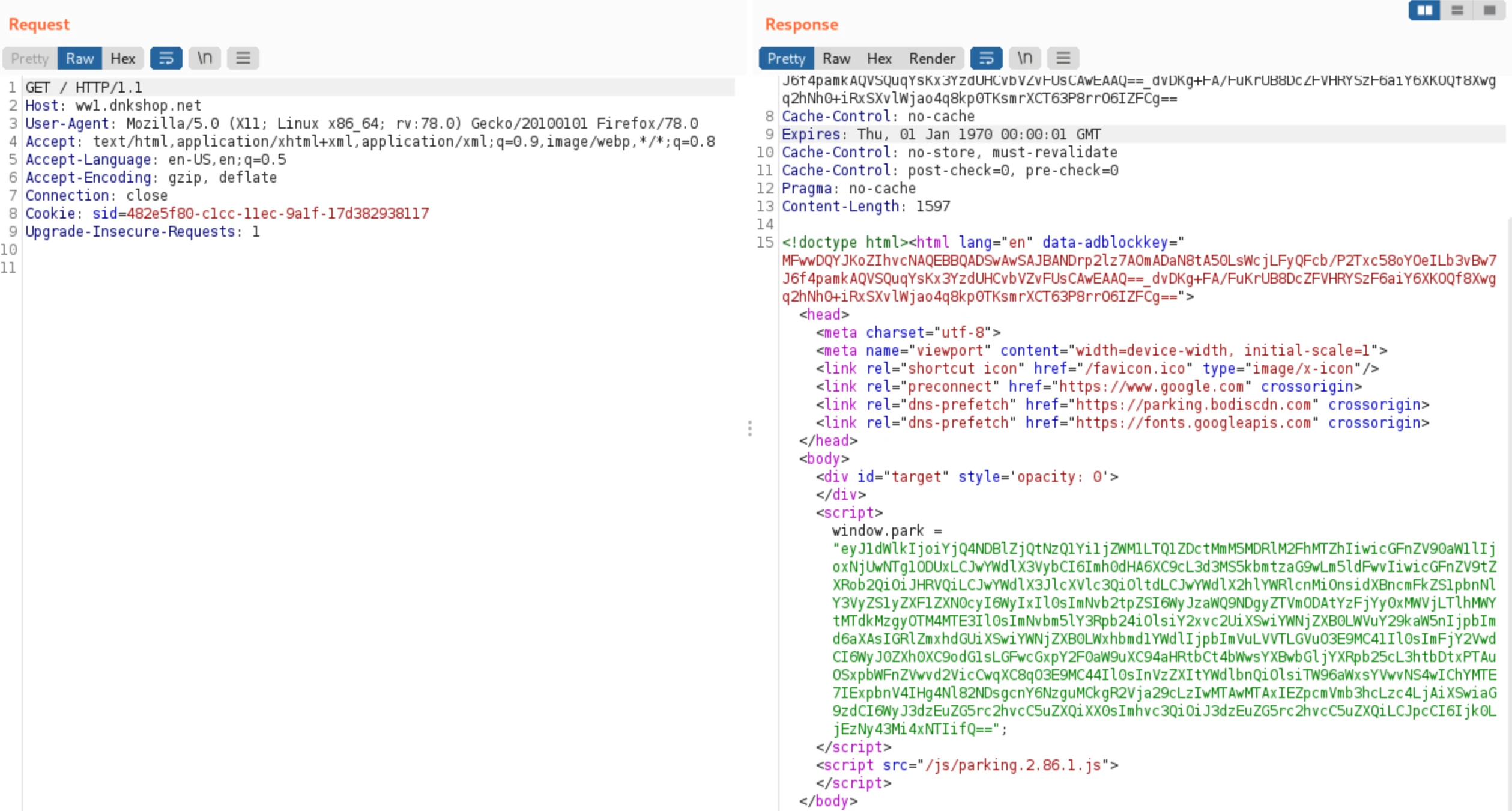
Decoding this gives a JSON response basically building the request headers and contains my IP (which in this instance is going through a VPN).
I also checked out the JS file. It is very long and has mentions to bodis
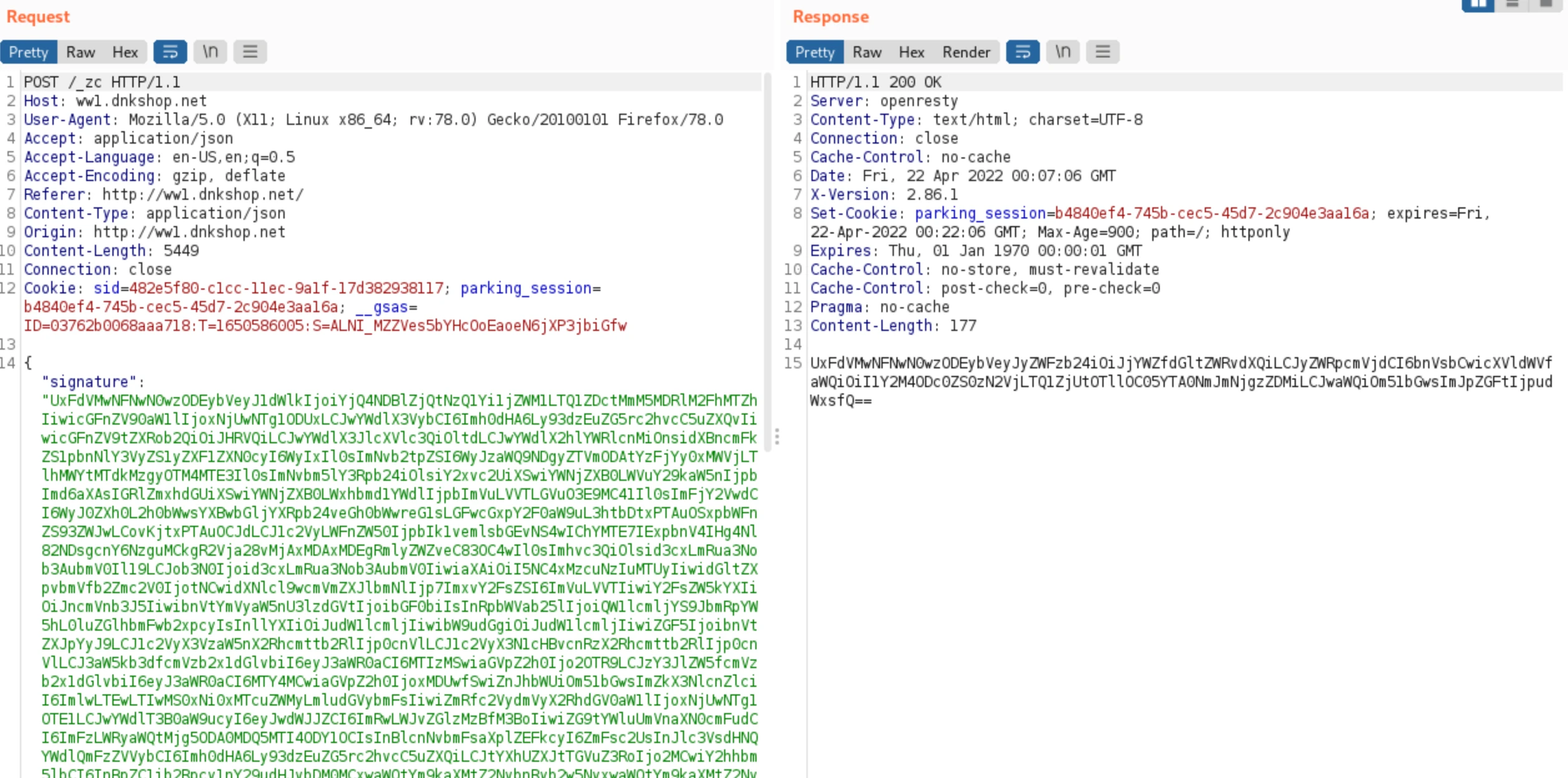
Next, I am redirect and it makes two POST requests on the www1<dot>dnkshop<dot>net domain, to /_fd first:
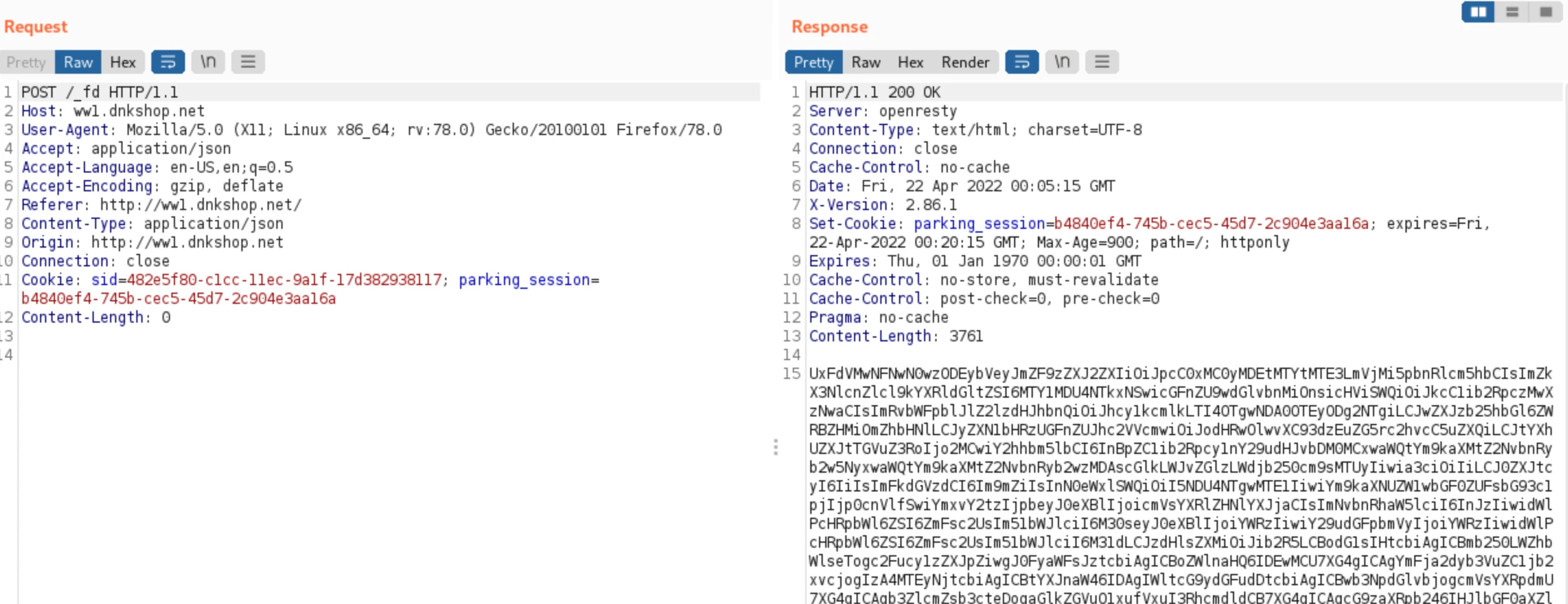
Which then appears to take that content and use it as a signature in it's request to /_zc:
I then get redirected to GoDaddy's purchase page to try and buy the dnkshop domain myself:
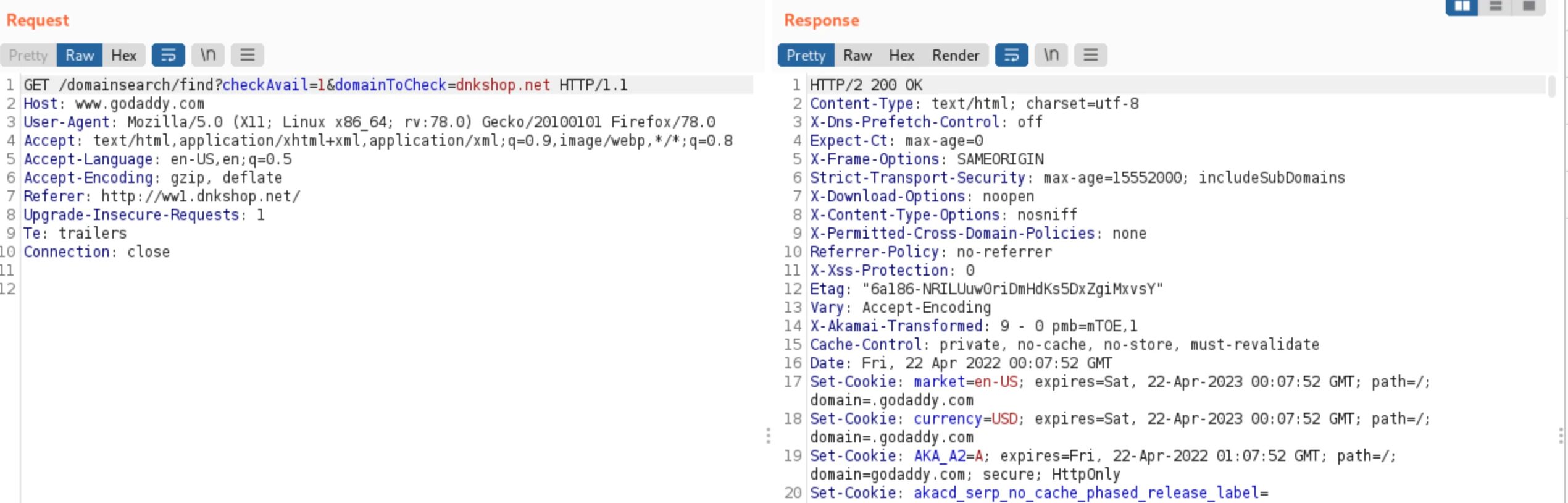
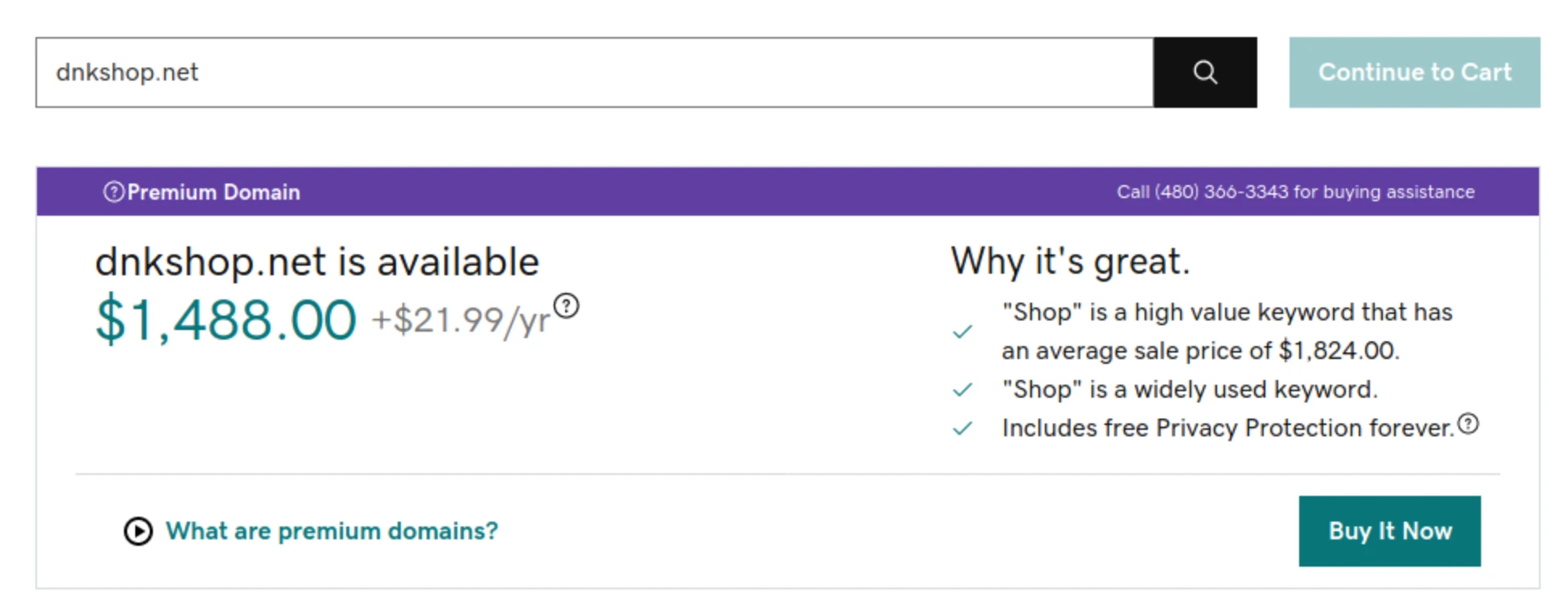
Which it does happen to be available, interestingly. My assumption is after tracking all of the requests, it perhaps is hoping the end-user is signed into GoDaddy and maybe the cookies would try to auto-purchase the domain for you?
Attempt 3: ww2
It's interesting because each time I click the link, the URL it first sends me to appears to change. Let's check this rabbit hole.
It has further tracking cookies that track the sale form:
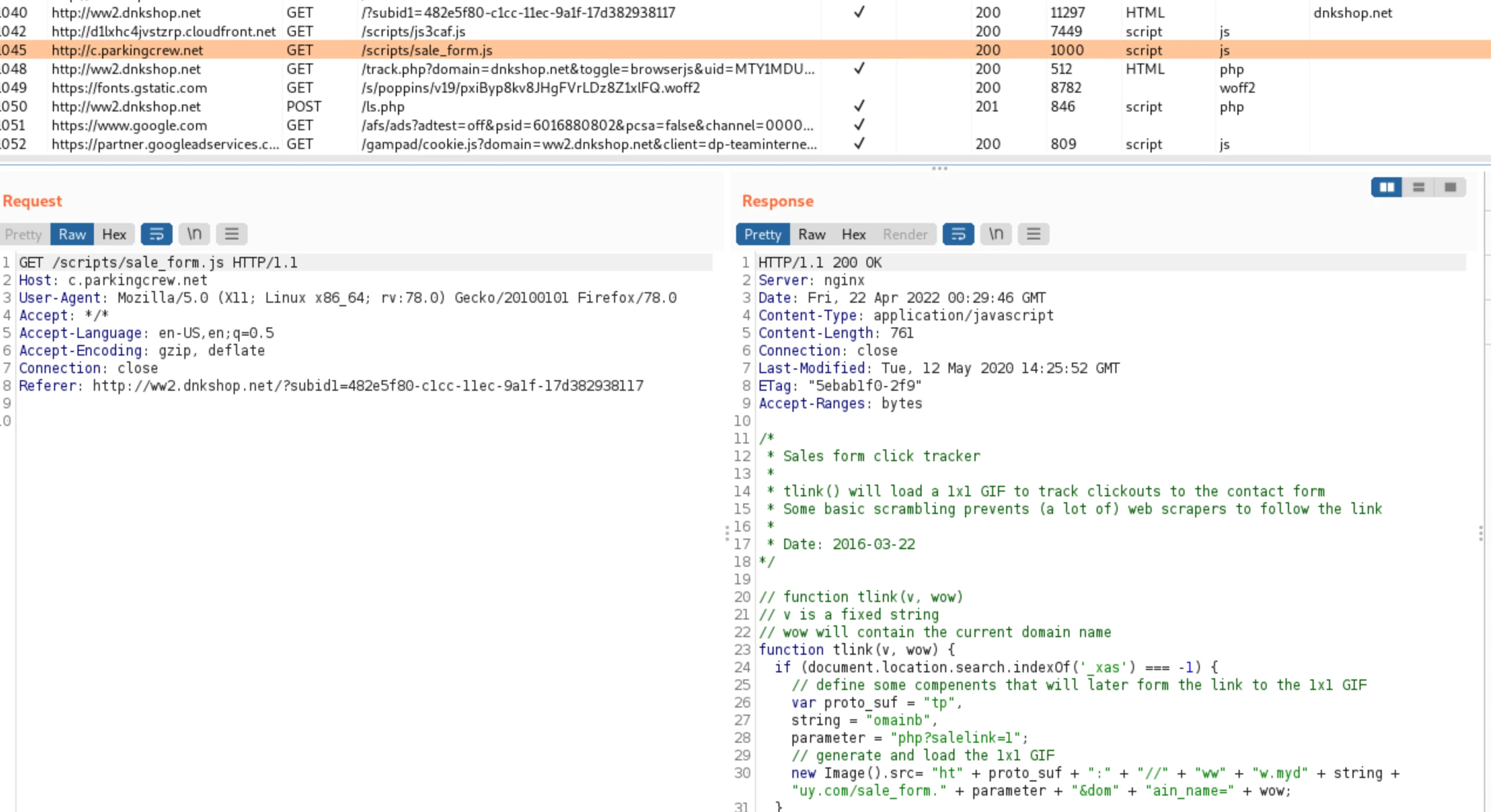
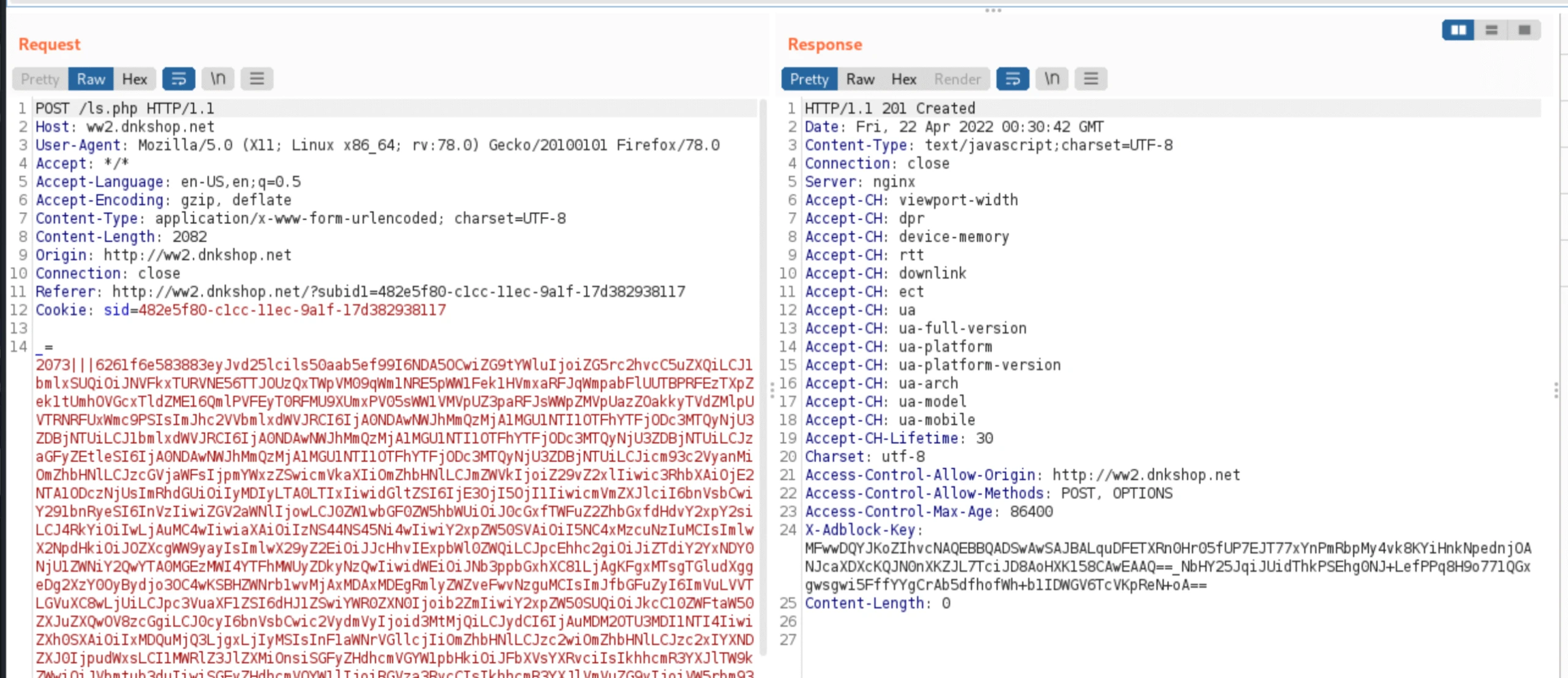
And it also sends a big blob of data to itself on the /ls.php endpoint:
Further Attempts
I ran it a bunch of different times and it would vary between "domain for sale" pages, but once I got redirected through another few hoops to a "job posting" page.
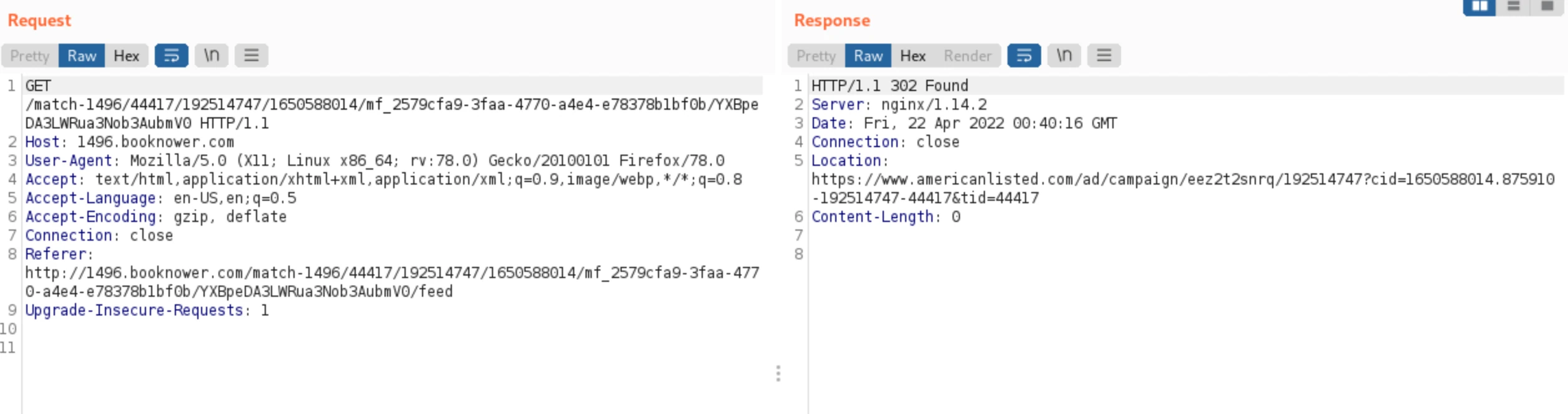
From the booknower website again, but now to american listed:
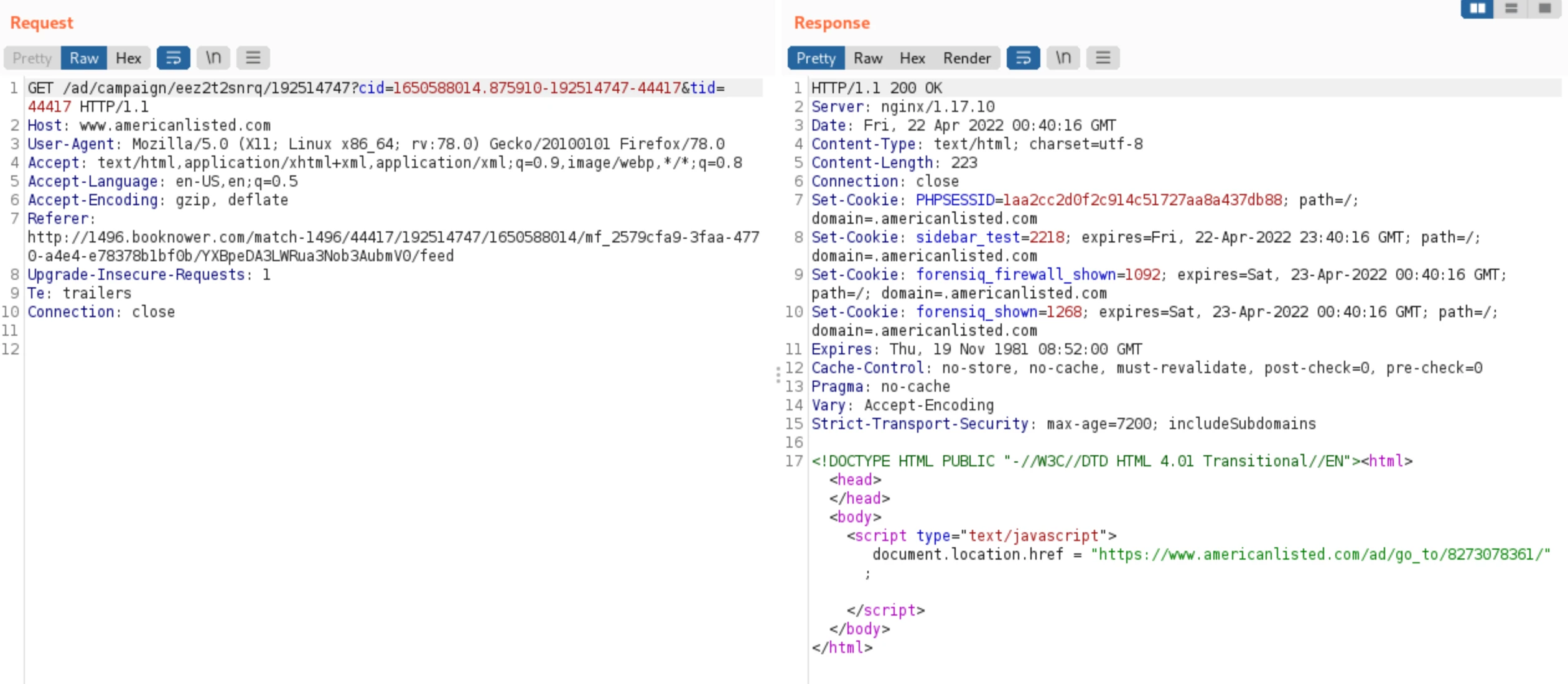
Which then redirects to an ad campaign, that redirects me to jobs in New York (where my VPN is currently set):
Then it hops through a bunch of other trackers and a jobhelper
Conclusion
This URL is definitely odd. It always will redirect to the dnkshop whois clearly indicates it's registered and valid until 2023:
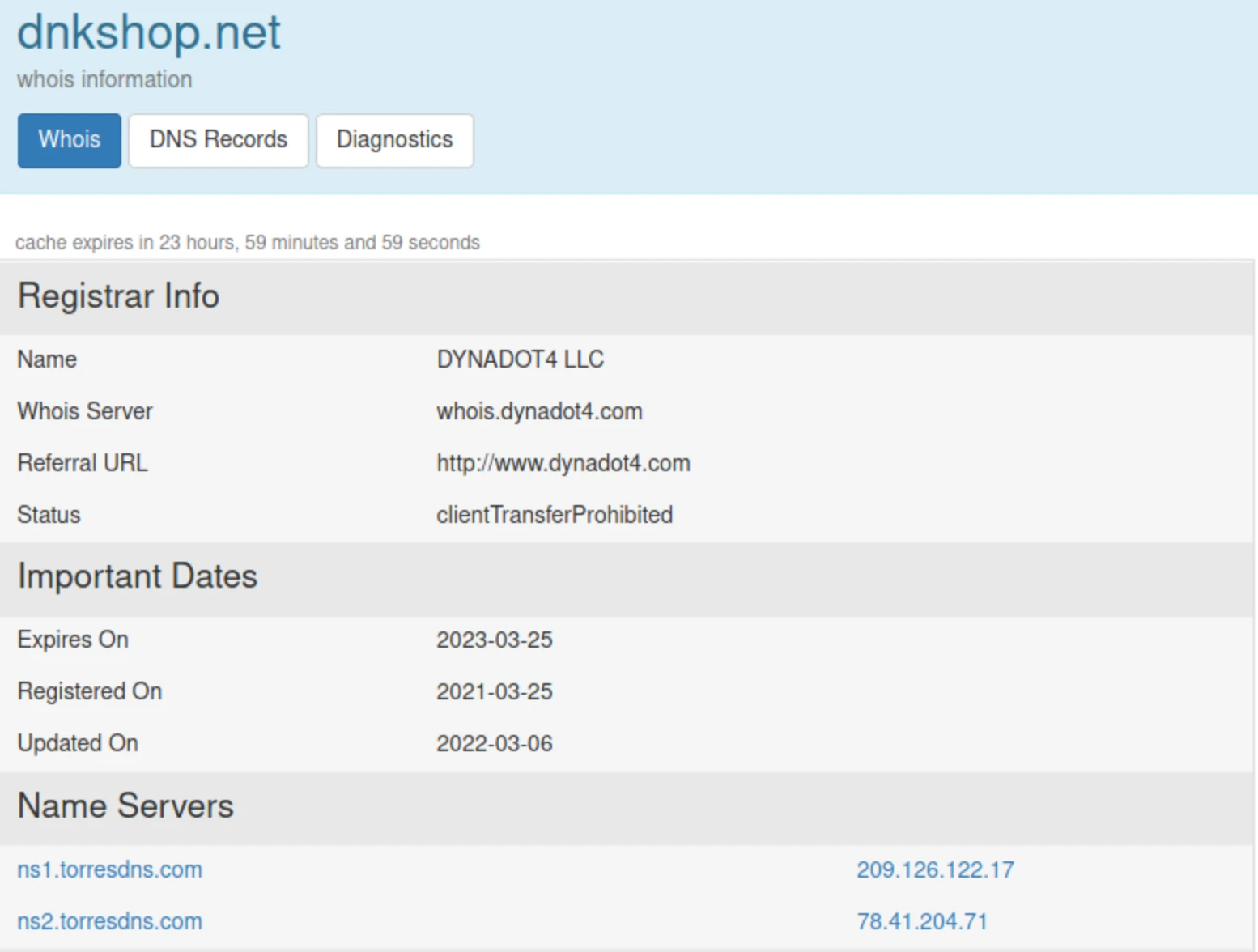
whois record
Only on rare occasions could I get it to redirect me to some other site such as the job posting site. It must have some sort of randomization feature on where it redirects you. I have tried clearing my cache/cookies each time as well but the majority of the time I always got some sort of for sale page. The "for sale" page was some variation of the following:
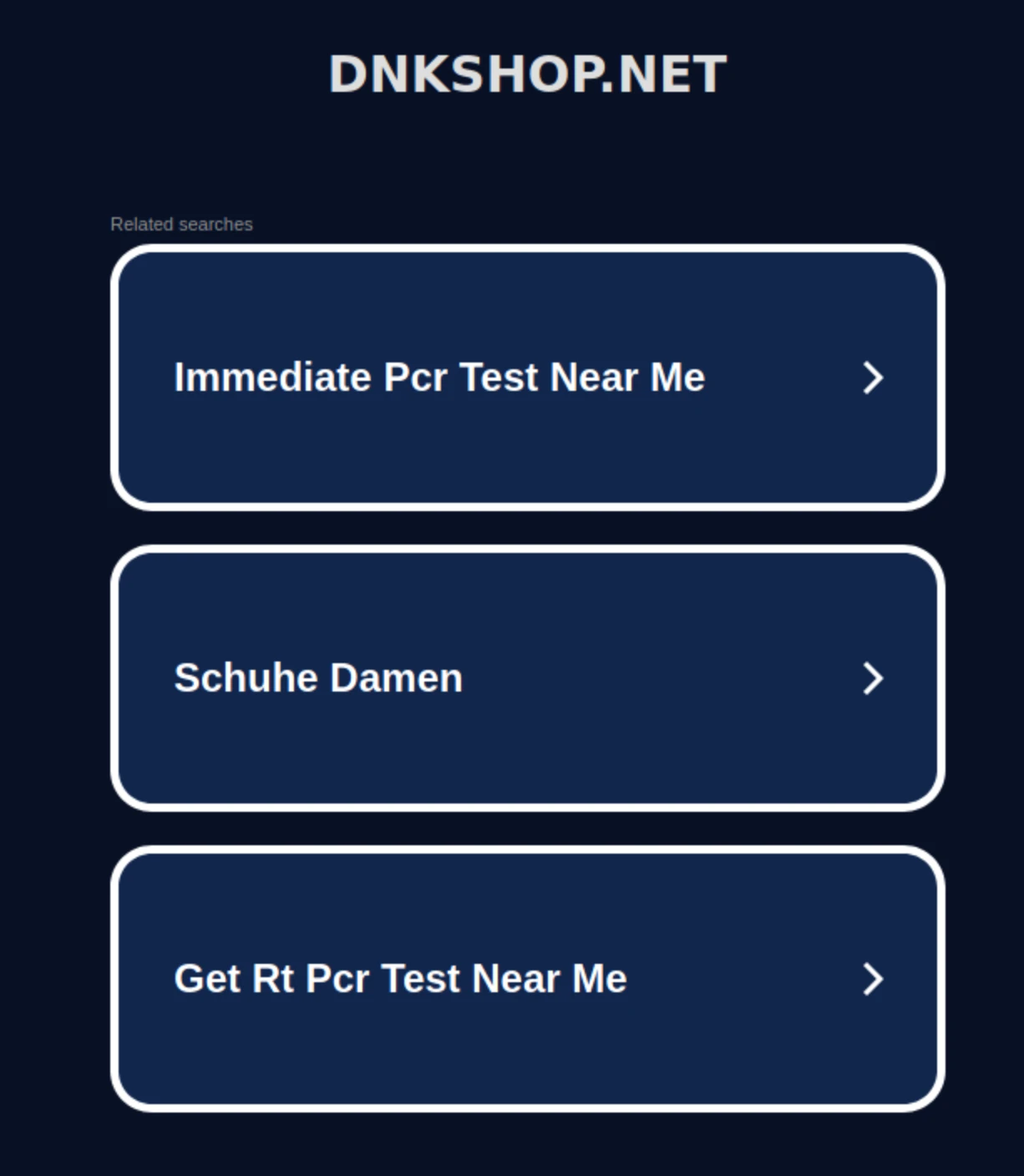
random google ad links
Clicking any of the links just grabbed info from google but kept you on the site. Presumably they earned a few cents for each click as ad revenue maybe? It's definitely an odd link as sometimes it would fire out to someplace else, but mostly would just show for sale.