I decided to try and get into my own malware analysis, but I needed to create my own lab for safe testing. I wanted to outline how I set mine up.
Update 2 Mar 2022: I migrated from VirtualBox to Parallels 16 and I get MUCH better performance, even when running both boxes simultaneously. Windows 10 is WAY more fluid and my resource utilization is way down. I am considering upgrading to a new M1 Mac, and Parallels 17 + Windows 11 ARM is the only virtualization software available so this is my test run with Parallels as a hypervisor.
Quick Overview
- Main Device: MacBook Pro 2017
- Intel i7 2.9 GHz Quad-Core Processor
- 16GB 2133 MHz LPDDR3 RAM
- Radeon Pro 560 4 GB Graphics
- 500 GB internal SSD, 1TB external Samsung SSD (MU-PC1T0T)
- Parallels Virtual Machines
- Linux Box running REMnux v7 (Ubuntu v20.04.3 LTS)
- 4096 MB RAM
- 128 MB VRAM
- 50GB VDisk on the external SSD
- 2 Network Adapters
- One adapter configured with static IP of
10.10.2.2(private network. no internet) - One adapter using Shared Network (DHCP) for internet access
- One adapter configured with static IP of
- Windows Box running un-activated Windows 10 Pro
- 4096 MB RAM
- 128 MB VRAM
- 50GB VDisk on the external SSD
- 1 Network Adapter
- Configured with static IP of
10.10.2.3, default gateway and DNS set to go back to REMnux box of10.10.2.2
- Configured with static IP of
- Linux Box running REMnux v7 (Ubuntu v20.04.3 LTS)
Setup
VM Setup - Phase 1
- Create a new virtualbox VM. Download the .ova file from REMnux here and install.
- Run
remnux upgradeand waited a while to ensure it was all up-to-date. I also ransudo apt-get update && sudo apt-get upgradejust to be sure. - Shut down the VM and make a snapshot of latest patches
- Create a second virtualbox VM for windows. I downloaded a fresh .iso from Microsoft here and went through the setup. I provided it a key for Windows 10 Pro I found even though I had no actual intentions of activating.
- Download and install flare-vm tools from here. Wait for it to install then shutdown and save a snapshot
Network Setup
Now it's time for the network setup to get these two boxes communicating with each other.
In VirtualBox, add a new network adapter to both machines like so:
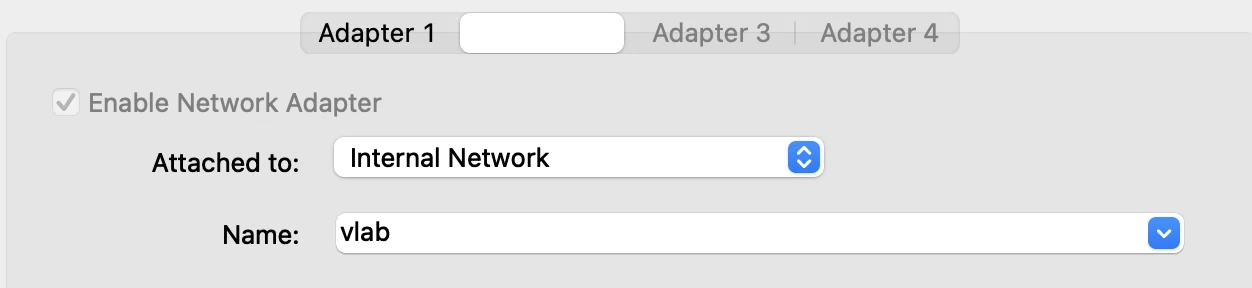
New Adapter
Make sure the name matches.
REMnux Network Setup
REMnux uses netplan for configuration. After adding the new adapter in the previous step, boot the VM back up and run ifconfig. There will be two enp0s# adapters, one of which will have an IP and the second doesn't have anything. For me, they were enp0s3 and enp0s8.
Run ls /etc/netplan to see the name of the configuration file that is being used. Mine was 01-netcfg.yaml so I can edit it with sudo nano /etc/netplan/01-netcfg.yaml. I created the enp0s8 adapter and saved it:
# This file describes the network interfaces available on your system
# For more information, see netplan(5).
network:
version: 2
renderer: networkd
ethernets:
enp0s3:
dhcp4: yes
enp0s8:
addresses:
- 10.10.2.2/24
Apply the changes with sudo netplan apply and now if you run ifconfig you will see the static IP for the new enp0s8 adapter:
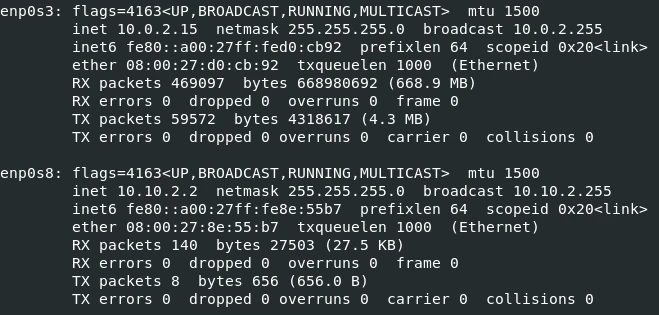
Our two adapters
Windows Network Setup
Navigate to the Network Connections in Control Panel. Right click the Network Adapter, Click Properties. In the new window, find Internet Protocol Version 4 and click it, then click Properties.
The IP address can be anything, I chose 10.10.2.3 with a subnet mask of 255.255.255.0 ensure the first 3 octets match the octet range used for the linux box. Now the Default Gateway and Preferred DNS server need to point back to the same IP used for the linux box.
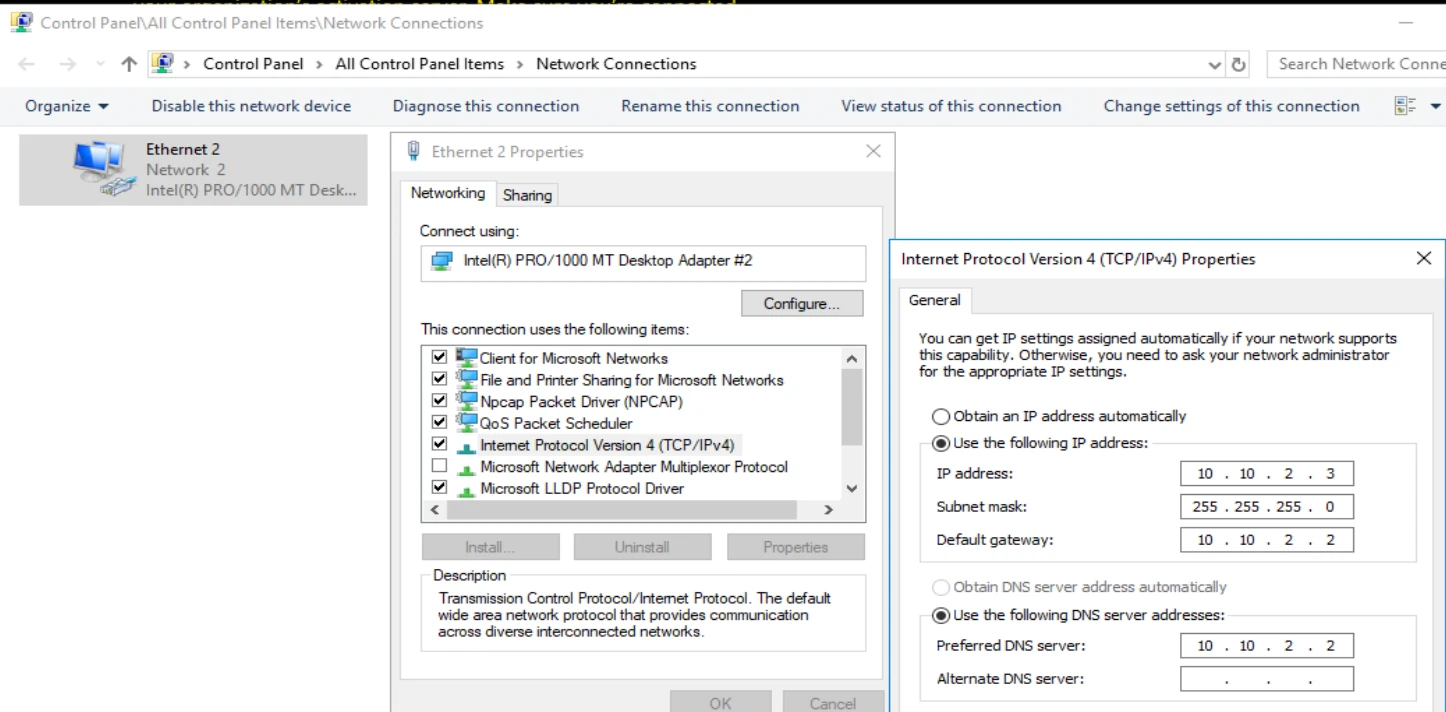
Completed Network Settings
REMnux Lab Preparation
Shutdown both boxes and create a snapshot. This will be where to return after doing any malware infections or if something goes awry. Returning to this point ensures we have upgraded boxes with the network setup properly.
To actually start properly capturing the data from the windows box into REMnux, we open two terminals and run a command in each. Be sure to replace the network adapter and IP with whatever you used for this linux box.
$ accept-all-ips start enp0s8
# After that command runs, next run the following (using the IP you set the box to)
$ sudo inetsim --bind-address 10.10.2.2
In a second terminal run:
$ sudo fakedns -I 10.10.2.2
Now we will have all network traffic that comes through our box captured. The fakedns will respond to every DNS call with its own IP. The inetsim will return an HTML page whenever the website is then requested.
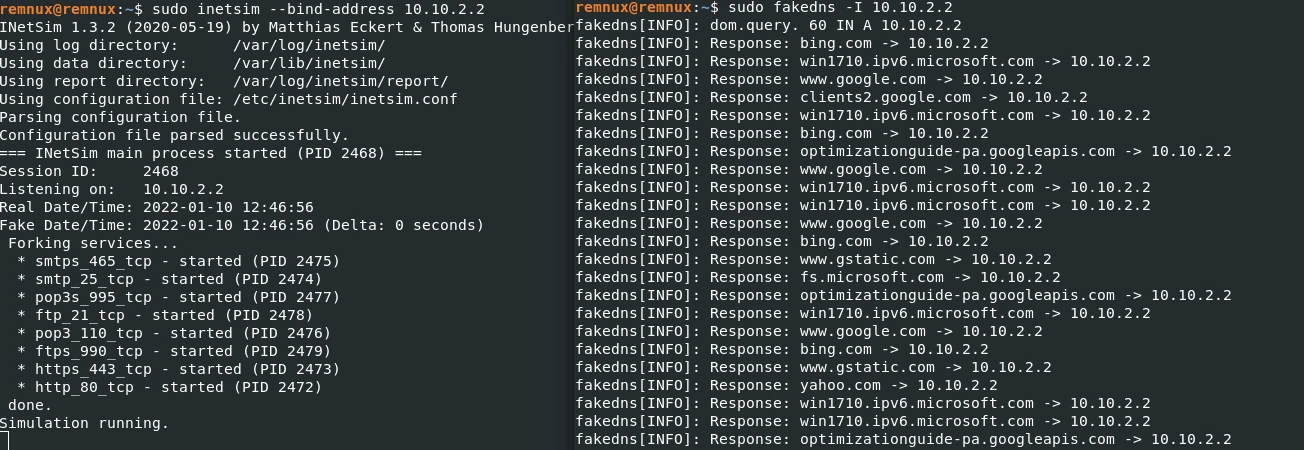
Our running services, note all of the DNS hits in the terminal on the right being redirected to ourselves
Open Wireshark on the REMnux box and choose the same enp0s8 adapter, here we can monitor all the queries being made from our windows box! Test it by trying to open anything on the Windows box:
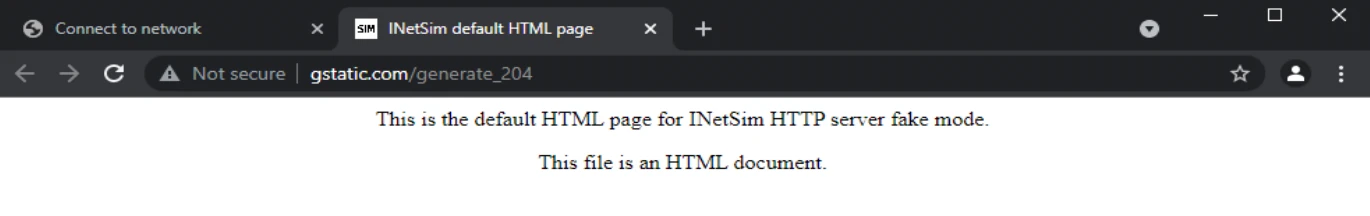
Success!
This query should make a hit on the DNS terminal and in Wireshark. Now we are ready for any malware to come through and try to make network requests
Windows Preparation
On our windows box, we can start up procmon right before we execute the malware to keep track of what processes are changing in the background. Once we let it run for several minutes, Save the file as .csv and send to procDot to help clean it up and generate a process graph!
procDot also needs windump.exe, which can be installed from here, and dot.exe can be found in C:\Program Files\GraphViz\bin\dot.exe.
Ready
Now we have snapshots, network communication and tracking and process tracking. We are ready to roll!
References:
- Building a Custom Lab: https://www.sentinelone.com/labs/building-a-custom-malware-analysis-lab-environment/
- Configuring Network on Ubuntu: https://serverspace.io/support/help/configuring-the-network-interface-in-ubuntu-18-04/