Link: https://app.hackthebox.com/challenges/reminiscent
Our unzipped folder gives us a Resume.eml, imageinfo.txt and flounder-pc-memdump.elf memory dump file.
Let's check out the email message. I ran cat Resume.eml which nets us:
Return-Path: [email protected]
Delivered-To: [email protected]
Received: (qmail 2609 invoked by uid 105); 3 Oct 2017 02:30:24 -0000
MIME-Version: 1.0
Content-Type: multipart/alternative;
boundary="=_a8ebc8b42c157d88c1096632aeae0559"
Date: Mon, 02 Oct 2017 22:30:24 -0400
From: Brian Loodworm [email protected]
To: [email protected]
Subject: Resume
Organization: HackTheBox
Message-ID: [email protected]
X-Sender: [email protected]
Received: from mail.madlab.lcl (HELO mail.madlab.lcl) (127.0.0.1)
by mail.madlab.lcl (qpsmtpd/0.96) with ESMTPSA (ECDHE-RSA-AES256-GCM-SHA384 encrypted); Mon, 02 Oct 2017 22:30:24 -0400
--=_a8ebc8b42c157d88c1096632aeae0559
Content-Transfer-Encoding: 7bit
Content-Type: text/plain; charset=US-ASCII
Hi Frank, someone told me you would be great to review my resume..
Could you have a look?
resume.zip [1]
Links:
[1] http://10.10.99.55:8080/resume.zip
We can see a link to a zip file on a remote server from the email. It is named resume but the extension is a .zip instead of a .docx or .pdf which should have been the first indicator to leave the attachment alone.
Next inside our package was an imageinfo.txt that provides information on the flounder-pc-memdump.elf memory file:
Suggested Profile(s) : Win7SP1x64, Win7SP0x64, Win2008R2SP0x64, Win2008R2SP1x64_23418, Win2008R2SP1x64, Win7SP1x64_23418
AS Layer1 : WindowsAMD64PagedMemory (Kernel AS)
AS Layer2 : VirtualBoxCoreDumpElf64 (Unnamed AS)
AS Layer3 : FileAddressSpace (/home/infosec/dumps/mem_dumps/01/flounder-pc-memdump.elf)
PAE type : No PAE
DTB : 0x187000L
KDBG : 0xf800027fe0a0L
Number of Processors : 2
Image Type (Service Pack) : 1
KPCR for CPU 0 : 0xfffff800027ffd00L
KPCR for CPU 1 : 0xfffff880009eb000L
KUSER_SHARED_DATA : 0xfffff78000000000L
Image date and time : 2017-10-04 18:07:30 UTC+0000
Image local date and time : 2017-10-04 11:07:30 -0700
We can use the Volatility framework to investigate this file.
# view running processes
$ vol.py pslist --profile=Win7SP1x64 -f flounder-pc-memdump.elf
We see two powershell.exe processes running from the above command. One at 496 and one at 2752.
# scan the active network connections
$ vol.py netscan --profile=Win7SP1x64 -f flounder-pc-memdump.elf
...
0x1fc04010 TCPv6 -:0 6890:8300:80fa:ffff:6890:8300:80fa:ffff:0 CLOSED 2752 powershell.exe
0x1fc04490 TCPv4 10.10.100.43:49246 10.10.99.55:80 CLOSED 2752 powershell.exe
0x1fc15010 TCPv6 ::1:2869 ::1:49237 ESTABLISHED 4 System
0x1fc3d320 TCPv4 10.10.100.43:49247 10.10.99.55:80 CLOSED 2752 powershell.exe
We can see a few closed connections to the same IP that the file was downloaded from on the PID 2752, powershell.exe process.
# search for resume files open
$ vol.py filescan --profile=Win7SP1x64 -f flounder-pc-memdump.elf | grep resume
Volatility Foundation Volatility Framework 2.6.1
0x000000001e1f6200 1 0 R--r-- \Device\HarddiskVolume2\Users\user\Desktop\resume.pdf.lnk
0x000000001e8feb70 1 1 R--rw- \Device\HarddiskVolume2\Users\user\Desktop\resume.pdf.lnk
We do have two files open, lets dump the files and see what we can derive from them:
# dump files at the specified offset to the current directory
$ vol.py dumpfiles --profile=Win7SP1x64 -f flounder-pc-memdump.elf -Q 0x000000001e8feb70 -D .
We can use strings on the files and a bunch of base64 appears. I threw the output into cyberchef and it returns a command with period delimitation and another base64 string:
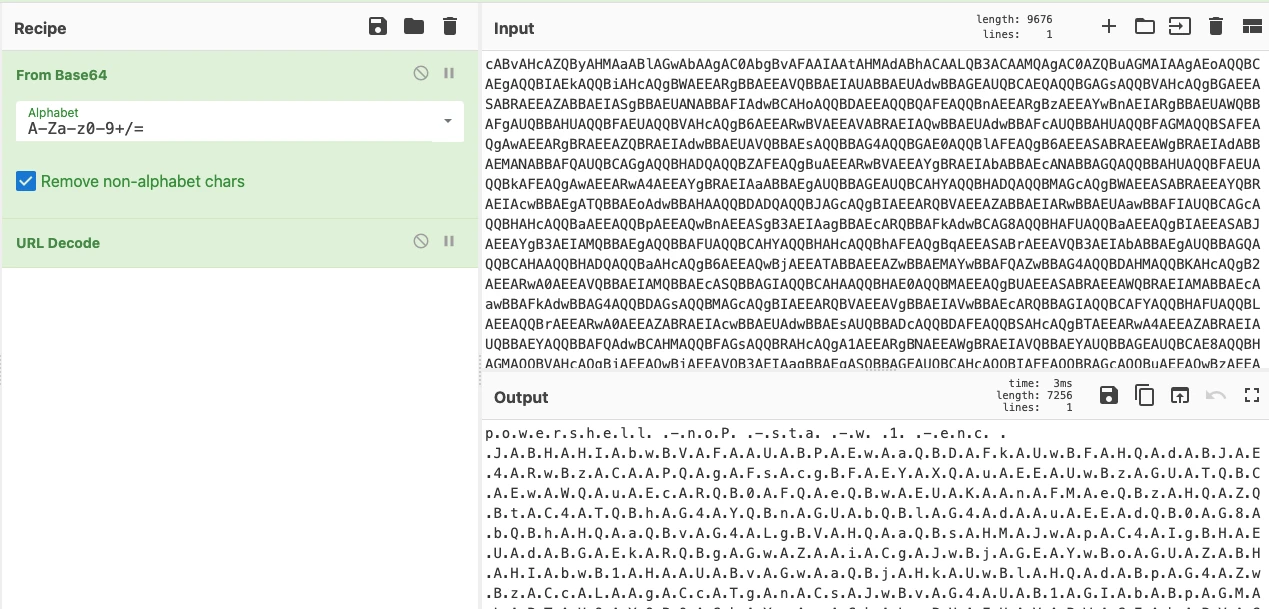
from base64
After a quick google search, the period can be a sign of UTF-16(LE) encoding, according to this StackOverflow post. So, if we pass this through a Decode Text - UTF-16LE (1200) module, it removes the periods and we can copy the new base64 string and paste it.
After decoding the new string, we see the actual powershell code. Down near the very bottom is a $flag variable with our flag.